Endpoint Detection and Response
Last Updated:
Analyst Coverage: Fran Howarth
Endpoint detection and response (EDR) provides visibility into activity occurring on the network and endpoints by continuously monitoring activity for behavioural patterns that appear to be suspicious or anomalous. Data captured provides rich contextual information related to a threat to enable more efficient, prioritised remediation. EDR technologies not only collect data, but use preconfigured detection models to enable teams to proactively hunt for threats before they can impact the organisation.
Why is it important (hot)?
Endpoint protection (EPP) technologies have traditionally been focused on preventing malware from infecting endpoints, which are proliferating rapidly in number and which are now used by adversaries as a preferred threat vector. They were focused on preventing infection, rather than on detecting threats that have gained a foothold on the network and removing them. EDR technologies enable organisations to move from a reactive to a proactive security stance that enables detection of even advanced, previously unseen threats, providing context regarding how the threat has impacted the network so that remediation can be prioritised to focus on the most critical events.
How does it work?
One of the core features of EDR technologies is that they monitor endpoint and network events, looking for suspicious or anomalous behaviour from both internal and external sources that does not conform to normal patterns of behaviour from devices or users. Data pertaining to events uncovered is stored in a central database so that it can be analysed to provide insight that can drive more efficient and automated incident response. By taking into account context surrounding events associated with device and user behaviour, the scourge of false positives can be greatly reduced so that remediation action can be taken in a more efficient manner.
Threat intelligence is key to EDR, helping 81% of organisations to improve their prevention, detection and response capabilities, according to the SANS Institute. Threat intelligence can be gathered from within the network and endpoints, as well as from feeds that analyse vast swathes of samples collected in the wild as well as submitted by organisations that have encountered them. In order to effectively make sense of the huge number of intelligence events, machine learning enables the analysis of big data sets to spot hidden patterns such as indicators of compromise that could indicate a threat, even where no alert has been raised. Threat and malware variants uncovered are stored in a knowledge base to enable automated remediation when the same or a similar threat is detected again. The value of machine learning increases over time as the knowledge base grows. When combined with behavioural analysis, organisations can even uncover events that evade machine learning capabilities.
The use of threat intelligence and automated detection is key to threat hunting enablement, whereby security analysts proactively search for advanced threats that evade existing security solutions, helping to reduce exposure to and improving the accuracy of response to threats in order to reduce the likelihood of security breaches.
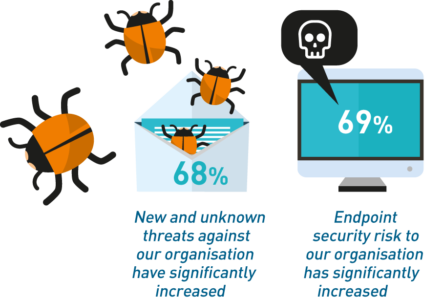
The majority of organisations report that they are seeing increased risk associated with endpoints (Figure 1). Whereas many organisations feel confident in their ability to protect against known malware, they are generally less so with regard to detecting and preventing previously unseen threats. Many are looking to reduce the dwell time of threats that have already impacted their network in order to reduce the ensuing damage. This is causing a large shift from deployment of reactive, preventative endpoint controls to proactive technologies such as EDR.
According to research published by Credit Suisse, incorporating data from Gartner, the EDR market will grow 17 times faster than the EPP market to 2020, reaching a value of $1.5 billion in 2020. It estimates that by 2020, 60% of IT security budgets will be dedicated to detection and response, rather than protection, which is a considerable shift from just 10% in 2013. This is because organisations are seeing the inevitability of breaches. Even though some EPP solutions, such as next-generation anti-virus, have some capabilities for detection and response, organisations are looking for more robust features.
Quotes
“As every IT professional knows, there are no solutions capable of stopping 100% of threats. That’s why EDR solutions exist to deal with the advanced threats that manage to get through. Though relatively new, EDR is maturing and evolving quickly as vendors work to protect endpoints against an equally fast-moving threat landscape.”
SANS Institute
“EDR products are powerful tools that provide a play-by-play of exactly what happened on a computer during and after an attack. The insights can reveal details of how a hacker mounted an attack and moved throughout systems. Programmed with the right rules, EDR products can also cut off potentially infected machines from the network and stem further damage.”
BankInfoSecurity
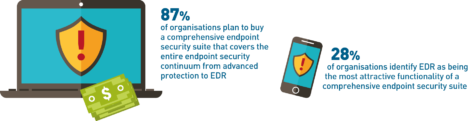
Whilst some may see EDR as a standalone technology in its own right, organisations are increasingly realising the need for integrated products or platforms that provide visibility across networks, consolidated into one single pane of glass view. Many will see the greatest value when EDR is integrated with complementary security products, including security information and event management systems, user and entity behaviour analytics, incident response orchestration and threat intelligence feeds in order to improve overall capabilities for threat detection and response, vastly improving the efficiency of their security operations centres.
Many EDR vendors provide APIs for such connectivity, whilst others are developing their own suites of integrated products. Alternatively, organisations with less mature security capabilities are availing themselves of the growing number of managed services providers that offer capabilities in EDR and complementary areas.
The Bottom Line
Every organisation benefits from the productivity enabled by endpoint devices, but these are a major threat vector and they need to assert control over them. EDR is ideal for asserting that control and for reducing exposure to security breaches.
Solutions
These organisations are also known to offer solutions:
- Absolute Software
- Broadcom
- Carbon Black
- CrowdStrike
- Cybereason
- Cylance
- Cynet
- Digital Guardian
- Fidelis Cybersecurity Solutions
- FireEye
- McAfee
- Nyotron
- Palo Alto (Secdo)
- Qualys
- SentinelOne
- Symantec
- TrendMicro