Security Response Orchestration
Last Updated:
Analyst Coverage: Fran Howarth
Orchestration builds on automation capabilities. Full automation is not appropriate in all circumstances. When dealing with complex incidents, human knowledge can help to better understand context so that more informed decisions can be taken. Security response orchestration aims to provide that in an effective manner.
Why is it important (hot)?
Organisations are increasingly being placed under pressure to respond to an ever growing volume of increasingly complex cyber attacks that put their organisations at risk. In response, organisations have implemented a variety of security controls to increase their defence capabilities, but this does not solve all the issues that they face. Rather, greater focus on an effective response strategy is needed.
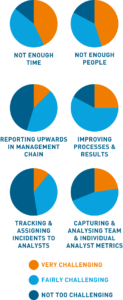
The vast majority are under pressure owing to the worldwide shortage of skilled security personnel, increasing the desire to automate tasks where possible to make the most of the limited skilled resources that they have available. Many traditional incident response controls throw up enormous volumes of alerts, many of which are irrelevant, making it hard to determine which constitute an real threat so that response actions can be based on actual need and prioritised according to the severity of the threat the organisation faces.
For many years, incident response automation has been seen as a panacea to reach for, removing much of the manual labour involved in responding to a security incident. Tasks that are suited for automation are those for which the outcome is defined and relatively certain, such as deploying antivirus defences, authentication controls, automated patching and firewall management. However, there is a significant amount of uncertainty associated with cybersecurity, which requires that the response to a situation must be dynamic and agile. Adversaries are not only malicious, they tend to regularly change tack in terms of their tactics to gain the upper hand against defenders. A response system that can be adapted to needs and current circumstances is required. Orchestration provides the answer to this—it uses automation where possible, complementing this with human coordination where necessary to achieve the desired result.
How does it work?
Security response orchestration helps organisations to respond effectively to data related to security events that has been gathered, correlated and analysed from multiple sources throughout the network. Building on automation capabilities, the emphasis of orchestration is on utilising the knowledge of humans where an outcome is unsure to make the entire response process more efficient and effective.
With security response orchestration, possible responses to security incidents are often codified in playbooks that outline processes required for a coordinated response following predefined steps based on the nature of the incident. Something to look for is the provision of information related to regulatory compliance requirements that can be mapped to obligations that must be met to the response actions being taken to avoid any situations of non-compliance.
To make orchestration more effective, threat intelligence updates are required for providing context into the nature and severity of an incident. These help to supplement alerts with relevant context regarding the details of the attack.
Machine learning applied to historical responses to threats, taking into account the effectiveness of the human response rather than just relying on historical data of what occurred, is a core facet of many orchestration technologies. It enables automation capabilities to be built based on the results of previous investigations in a proactive manner, helping to improve an organisation’s overall security posture.
According to the Ponemon Institute, amongst enabling security technologies, automation, orchestration and machine learning provides the third largest ROI at 17.1%, providing average annual savings in the region of $2.2 million among organisations that it surveyed.
Among the core uses cases for security response orchestration are alert enrichment and prioritisation, and endpoint containment. It provides for accelerated response to cyber attacks, increased productivity for the security operations centre, an improvement in the breach notification process, which is increasingly being required by regulations, by facilitating the mapping of actions taken to requirements for safeguarding privacy, and an ability to alleviate skills shortages. It aids organisations by reducing the mean time to recovery from serious security incidents, which can remain unidentified and unresolved on a network for weeks if not months, which can result in the overall damage to the organisation skyrocketing
Quotes
“The key to effective incident response is having the right combination of people, processes and technology.”
Infosecurity Magazine
“Some 90% of organisations plan to deploy, or have already done so, automation and orchestration technologies. More than one-third consider orchestration a priority over automation.”
ESG
Many organisations have implemented security information and event management (SIEM) systems or use SIEM services from a managed service provider. However, SIEM systems by themselves have come to be seen as unwieldy, with much manual labour needed for analysing the results of the analysis, and are further criticised since they perform poorly with regard to unknown threats and detection of insider threats.
To deal with these limitations, technology vendors have been developing innovative complementary technologies, including advanced security analytics, user and entity behavioural analytics, threat intelligence information and security response orchestration capabilities. Some orchestration capabilities are provided within integrated suites, whilst others are standalone capabilities. As the market continues to ensure, more and tighter integrations are to be expected.
The Bottom Line
Security is no longer an insurance policy; it can be life or death for many organisations. With the complex threat landscape we face today, automation only goes so far. Orchestration provides the missing layer needed to face down even the most determined adversaries.
Downloads
Solutions
Coming soon.
Research
Coming soon.